pplelabs
HIPAA Compliance Checklist: Implementation & Free Template
The Health Insurance Portability and Accountability Act (HIPAA) sets the standard for how healthcare organizations safeguard Protected Health Information (PHI), but for technical teams, it often becomes the rulebook that defines day-to-day security architecture and operations. Whether you’re running an electronic health record (EHR) system, designing APIs for patient data exchange, or maintaining cloud infrastructure that stores PHI, the stakes are high. A single misstep can mean hefty fines, reputational damage, or worse, compromising patient trust.
That’s where a structured HIPAA compliance checklist comes in. Instead of scrambling to interpret the legal jargon, technical leaders can use a checklist to translate requirements into concrete, actionable steps: configure access controls, encrypt PHI at rest and in transit, monitor logs, and maintain clear audit trails.
In this blog, you’ll find a detailed breakdown of HIPAA requirements mapped into a practical checklist. We’ll also share a downloadable template you can adapt for your own environment, helping your teams stay audit-ready without drowning in documentation.
Key requirements under HIPAA
HIPAA is not a single law but a collection of interrelated rules that together define how healthcare organizations, their business associates, and their vendors must handle PHI. Each rule sets specific expectations: some high-level, others deeply technical.
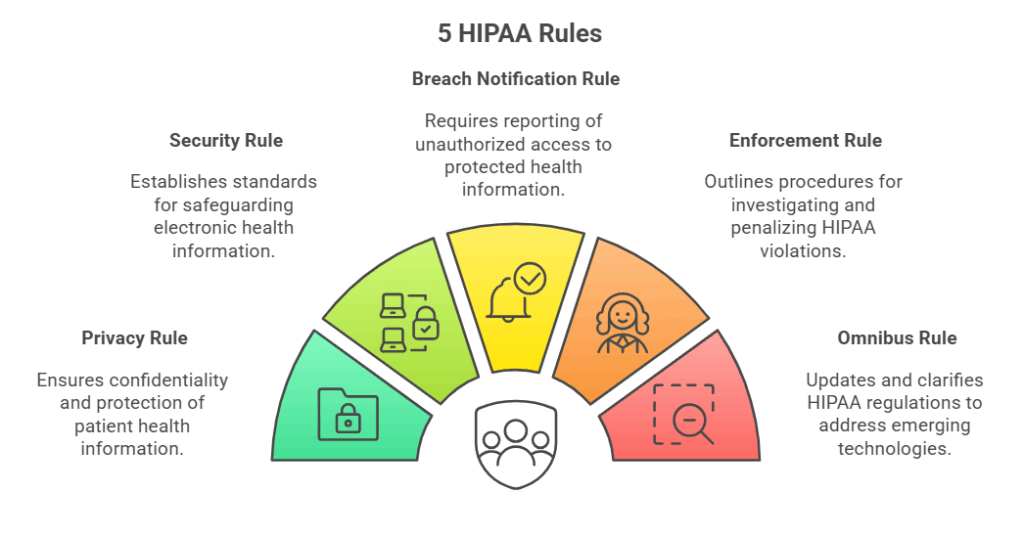
1. Privacy Rule
The Privacy Rule establishes the baseline for how PHI can be used and disclosed. It applies to all forms of PHI: electronic, paper, and oral. Although technical teams may not directly configure privacy policies, their systems are required to support them.
For technical teams, this means:
- Implementing role-based access so that only authorized personnel can access PHI.
- Logging disclosures and ensuring the system capabilities can honor patient rights, such as data access or amendment requests.
- Security Rule
The Security Rule focuses specifically on ePHI (electronic PHI). It outlines three primary safeguard categories:
- Administrative safeguards: These cover risk assessments, workforce training, access management, and contingency planning.
- Physical safeguards: This involves controlling physical access to servers, devices, and facilities.
- Technical safeguards: These are critical system configurations, including access controls, audit logging, encryption, and integrity protections.
This rule dictates system configurations, monitoring, and cloud security practices, making it the rule with the heaviest technical lift. The Security Rule defines “how” PHI must be protected.
- Breach Notification Rule
This rule requires covered entities and business associates to notify affected individuals, the U.S. Department of Health and Human Services (HHS), and sometimes the media, after a data breach.
From a technical perspective, compliance with this rule requires:
- Implementing monitoring to detect unauthorized access quickly.
- Maintaining audit trails that can confirm or disprove PHI compromise.
- Documenting incident response steps to serve as proof of compliance.
- Enforcement Rule
The Enforcement Rule lays out how HIPAA is enforced by HHS, including investigation procedures, penalties, and resolution agreements. While this rule is not technical in nature, it strongly reinforces why precise documentation, automated monitoring, and thorough audit readiness are critical. Fines can quickly escalate when violations are tied to systemic negligence.
- Omnibus Rule
The Omnibus Rule, enacted in 2013, significantly expanded HIPAA’s scope. It clarified the responsibilities of business associates (such as cloud service providers, billing vendors, and SaaS partners), strengthened patient rights, and increased penalty structures. The key takeaway for technical teams is that vendors handling PHI are now directly accountable, and their integrations and configurations must meet all HIPAA standards.
pplelabs
HIPAA Compliance Checklist: Implementation & Free Template
Protection of All Health Information Formats
HIPAA compliance requires the safeguarding of Protected Health Information (PHI) across all formats: electronic, paper, and verbal.
The "Minimum Necessary" Rule
Covered Entities must limit the use and disclosure of PHI to the minimum necessary amount required to achieve the purpose of the disclosure or request.
Enforcement by Federal Agencies
The Office for Civil Rights (OCR) primarily enforces the HIPAA Privacy and Security Rules, while the Department of Justice (DOJ) handles criminal violations.
How to Implement HIPAA Compliance: A Step-by-Step Guide
Understanding HIPAA’s requirements is one step; translating them into daily technical operations is the next. The rules define what you must do, but the real challenge is figuring out how to do it within your specific environment. A structured, step-by-step approach is essential to address this challenge.
The following guide breaks the implementation journey into four clear phases. This is the practical path from policy to implementation, with checkpoints to keep you audit-ready and reduce the risk of costly missteps.
Phase 1: Foundation and Scoping
The initial phase is dedicated to defining the scope of your environment and establishing the necessary governance structure.
- Scope your environment and data flows: Map exactly where PHI and ePHI live, how they move across systems, and who accesses them. You must confirm whether your organization is a covered entity, a business associate, or both. Create a comprehensive list of all systems, APIs, cloud services, and data stores tied to PHI.
- Stand-up governance: Appoint a Privacy Officer and a Security Officer. Set up a steering group and agree on clear approval paths for all policies and exceptions. It is vital to keep minutes and decisions, as these records are crucial during enforcement reviews.
- Execute business associate agreements: Identify every vendor that creates, receives, maintains, or transmits PHI on your behalf. Execute BAAs that fully meet HIPAA content requirements and ensure you track renewal dates in a register.
Phase 2: Risk Management and Safeguards
This phase focuses on the core Security Rule requirements for risk analysis and implementing the necessary safeguards.
- Run a security risk analysis: Conduct a documented “accurate and thorough” risk analysis. This analysis must cover the confidentiality, integrity, and availability of ePHI. The process should include inventories, threat models, vulnerability scans, and a formal likelihood/impact scoring of risks.
- Build and execute your risk management plan: Translate identified risks into concrete mitigations, assigning clear owners and deadlines. Establish a process to track residual risk after treatment.
- Implement administrative safeguards: Apply policies for access authorization, provide security awareness training, implement sanction policies, establish incident response procedures, and develop contingency planning (which includes backup, Disaster Recovery (DR), and emergency mode operations).
- Implement physical safeguards: Secure facilities, restrict workstation access, and enforce clear policies for the handling and disposal of devices and media.
- Implement technical safeguards: Configure access controls, audit logging, encryption, automatic logoff, and integrity protections. Where HIPAA defines a safeguard as “addressable,” you must document your choices.
Phase 3: Operational Execution
The third phase ensures that compliance is integrated into daily operations through monitoring, documentation, and incident response.
- Document policies, procedures, and configurations: Maintain policies that are fully aligned with actual practices. Keep versioned evidence of configurations, system diagrams, and Standard Operating Procedures (SOPs). All HIPAA documentation must be retained for six years.
- Establish monitoring, logging, and audit trails: Enable logs for all critical access, admin actions, data exports, and failed logins across all systems. Centralize these logs, route them to a SIEM (Security Information and Event Management) system, and build alerts for anomalies.
- Prepare incident response and breach notification: Define clear intake, triage, and escalation paths. Conduct regular tabletop drills. For breaches affecting 500 or more individuals, notification must be sent to the affected parties, HHS, and possibly the media within 60 days. For smaller breaches, reporting is done to HHS annually.
- Vendor security and change control: Vet all vendors handling PHI. Confirm they adhere to least-privilege access and align contracts with your HIPAA obligations. Route any major system or vendor changes through a new risk analysis.
- Train your workforce and enforce sanctions: Provide mandatory training on PHI handling. Log attendance and strictly enforce sanction policies for violations.
Phase 4: Continuity and Assurance
The final phase ensures that safeguards remain effective over time and that the organization is ready for any audit.
- Test backups and recovery: Run periodic DR drills. Verify the integrity of all backups and measure your Recovery Time Objective (RTO) and Recovery Point Objective (RPO) performance.
- Perform periodic evaluations: Carry out technical and non-technical evaluations whenever your environment changes to confirm that safeguards remain effective. The findings from these evaluations must be fed back into the risk analysis process.
- Get audit-ready: Build an evidence matrix that maps every safeguard to its proof—this includes policies, screenshots, logs, BAAs, and incident response reports. This ensures you can answer auditor requests quickly and consistently.
As industry leaders, we are focused on driving innovation and solving problems every single day.
Common Pitfalls Technical Teams Face
Even with a clear roadmap, technical teams frequently stumble on the same issues. Recognizing these pitfalls upfront can save significant time and costly remediation later.
- Over-reliance on manual monitoring: Solely relying on manual log reviews or ad-hoc checks leaves too much opportunity for human error. HIPAA expects continuous, consistent monitoring of access and activity around PHI, which manual methods rarely provide at scale.
- Misconfigured cloud storage: Public cloud buckets, unmanaged IAM policies, or weak encryption defaults are a frequent source of PHI exposure. Teams often mistakenly assume that using a HIPAA-eligible service automatically ensures compliance, but configuration mistakes remain their direct responsibility.
- Incomplete vendor oversight: Business Associate Agreements (BAAs) alone do not guarantee security. If third-party tools or SaaS providers are not thoroughly vetted for technical safeguards (such as encryption, access logs, and breach response), your compliance program has a significant blind spot.
- Delayed breach detection and reporting: Without strong audit trails and alerting, teams may fail to detect unauthorized access quickly. The Breach Notification Rule sets a hard 60-day reporting window , and investigations lacking proper logging can drag on, risking non-compliance.
- Neglecting documentation during system changes: It is a common problem to apply new configurations or roll out infrastructure changes without updating the associated policies and procedures. This gap is often flagged in audits, where auditors compare system evidence against outdated documentation.
- One-time risk assessments: Treating risk analysis as a “once and done” activity instead of a recurring exercise creates blind spots. HIPAA requires evaluations whenever environments or operations change, not just during initial compliance setup.
How pplelabs Helps You with HIPAA Compliance
pplelabs simplifies HIPAA compliance by automating the collection of evidence and mapping HIPAA safeguards to over 1,500 pre-built controls. It continuously monitors your cloud and SaaS systems for misconfigurations. pplelabs also centralizes vendor risk reviews and BAAs, and organizes all audit-ready documentation in its Trust Vault, ensuring you are always prepared when auditors arrive.
Frequently Asked Questions (FAQs)
What is a HIPAA compliance checklist?
A HIPAA compliance checklist is a structured list of HIPAA requirements that have been translated into actionable steps for ensuring PHI is protected and that your organization is audit-ready.
Who is this HIPAA compliance checklist for?
This checklist is for healthcare providers, insurers, business associates, and vendors handling PHI. It is especially relevant for CISOs, CTOs, compliance, and IT security teams.
Is there a specific HIPAA compliance checklist for IT?
Yes, there is. It focuses on the technical safeguards like access controls, encryption, logging, backup and recovery, and monitoring.
How do I know my documentation is sufficient to pass the HIPAA compliance audit?
Your documentation is generally considered sufficient if every safeguard is backed by dated, version-controlled evidence (such as risk assessments, policies, training, logs, and BAAs) that is retained for at least six years.
Who is responsible for implementing and monitoring the HIPAA regulations?
Covered entities and business associates are responsible for implementation and monitoring, with day-to-day oversight provided by designated Privacy and Security Officers.
What are the HIPAA compliance requirements?
Compliance requires meeting the Privacy, Security, Breach Notification, Enforcement, and Omnibus Rules. This covers safeguards for PHI, risk assessments, workforce training, vendor agreements, and proper breach handling.
What are the penalties for breaching HIPAA?
HIPAA penalties follow a four-tier structure based on the level of negligence:
- Tier 1 (Unknowing): $141 – $71,162 per violation, capped at $2.1M annually.
- Tier 2 (Reasonable Cause): $1,424 – $71,162 per violation, capped at $2.1M annually.
- Tier 3 (Willful Neglect, corrected within 30 days): $14,232 – $71,162 per violation, capped at $2.1M annually.
- Tier 4 (Willful Neglect, not corrected): $71,162 – $2.1M per violation, capped at $2.1M annually.
In addition to civil penalties, criminal penalties can apply for intentional violations, ranging up to fines of $250,000 and imprisonment of up to 10 years for the most serious cases.